Why did Google Play ban the deceptive use of interpreted languages like JavaScript and Python?
To ensure and enhance the safety and privacy of the apps listed on its PlayStore, Google has added some security guidelines to its policy. Particularly, this action is to curb the deceptive use of interpretative languages- JavaScript and Python hold.
What is the reason behind this ban?
So, the Mintegral SDK is a popular Chinese mobile advertising SDK, available to the iOS and Android platforms. Now, it has a massive outreach, used by thousands of mobile apps and it receives hundreds of thousands of downloads in a month. SDK is used to monetize its apps with third-party ads.
The Synk security research team found two appalling activities Mintegral SDK was up- 1)It brought into light that Mintegral SDK was collecting excessive data and click hijacking. 2) A backdoor was found on the iOS version of the SDK that would permit it to execute remote code.
Method Swizzling was one of the techniques where it tried to replace the implementations of the UIApplication openURL and SKStoreProductViewControllerloadProductWithParameters methods at runtime and by doing this, it registers a custom NSURLProtocol class. Now, with these hooks, they spy on application users and gather all the information like opened URLS. and information about HTTP requests through the click the user did within that application. Now, these URLs and HTTP requests contained sensitive data and along with IDFA i.e. Identifier for Advertisers, the data would make Mintegral perform advertisement attribution fraud.
Advertisement Attribution Fraud
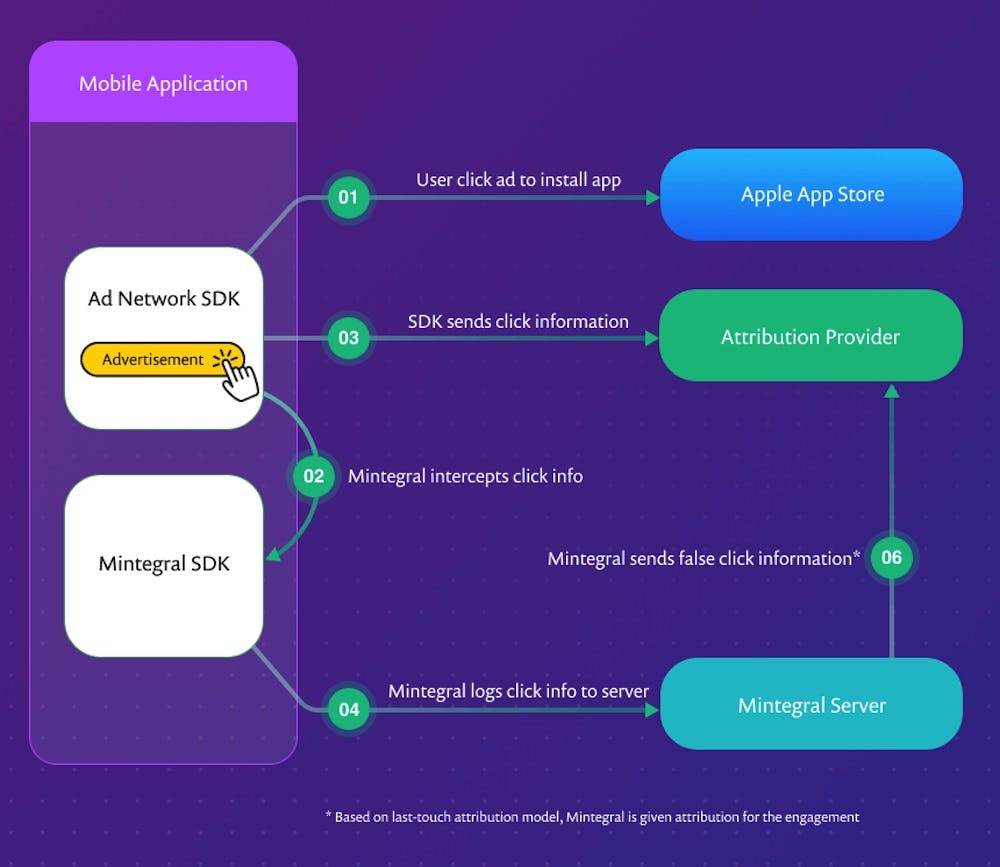
To monetize applications, advertising platforms are used. Ad platforms get money from advertisers for each installment as the user clicks their advertisement. So, multiple advertisement agencies are used and to estimate this attribution of how many clicks were assorted to which ad agency, there is a mobile measurement platform (MMP).
Now, Mintegral, through method swizzling was able to intercept all the URLs that were opened and in a quite sly manner, performed additional requests to an attribution provider hoaxing that the click was made on its advertisement rather than on the rightful one.
Alyssa Miller, Application Security Advocate at Snyk said,
“ The attempts by Mintegral to conceal the nature of the data being captured both through anti-tampering controls and a custom proprietary encoding technique, are reminiscent of similar functionality reported by researchers that analyzed the Tik Tok app.”
Now, the bigger issue is that the iOS users have no way of confirming whether the app they are using loads the Mintegral SDK and they have little means to safeguard the information and browsing habits. App developers can use the information from the Snyk report to detect the SDK and remove it or downgrade to a version where it does not get corrupted. However, they are still skeptical about the use of third-party libraries that could be misinterpreted and abused due to their functionality.
Hence, to make sure that this does not happen again, Google has enforced new security and privacy policy changes that will be enforced from October 15, 2021. Google shares that they would clarify the Device and Network Abuse Policy-
“to prohibit apps or SDKs with interpreted languages (e.g.. JavaScript) loaded at run time from violating any Google Play policies.”
One of the clauses of Device and Network Abuse states
that the app distributed through Google Play cannot in any way modify, replace or update itself using any method other than Google Play’s update mechanism. And by doing so, an app is not allowed to download executable code. However, it is not inclusive of those apps that run on virtual machines and has limited access to Android APIs- JavaScript in a webview or browser.
Also, along with this, the upcoming Android privacy change would include the ability to blank a device’s advertising ID. With that, a safety net would be provided for apps in the Play Store.
What is an advertising ID ?
It is a unique identifier to an Android device supplied by Google Play Services. The advertising ID is also used to profile the user of the device, as every app has access to the same ID.
So, advertising ID is issued by Google to all the apps that want to show targeted ads to their users. Now, if users opt-out of Targeted ads then the app gets no advertising ID for that user, and it is through the access of personal data, the app can access your searches and data to show targeted ads
Against a legal complaint, it has been argued that the advertising ID is personal data, and resetting it does not change anything. It just gets you a replacement ID. Google has accepted the idea of limiting ad tracking and the director of product management has posted that when the users opt-out of interest-based advertising, it would be removed and replaced with a string of zeros.
Hence, it is an attempt by Google to safeguard the apps to prevent revenue from getting stolen through advertising fraud and the breach of personal data that happens through method swizzling.